Security & Data Ownership
QuoteNode is built for organizations that treat commercial data as a strategic asset. Every architectural decision prioritizes isolation, auditability, and control.
Single-Tenant Isolation
Every QuoteNode instance runs in complete isolation. Your database, your file storage, your application process — none of it is shared with other customers. There is no multi-tenant data mixing, no shared connection pools, no risk of cross-tenant data leakage.
This is not a marketing claim about “logical separation.” It is physical isolation at every layer.
Self-Hosted Deployment
You choose where your data lives. Deploy on your own server, in a private cloud, or in a closed network with no internet access. QuoteNode operates fully offline — no telemetry, no analytics callbacks, no license server pinging.
The system ships as Docker containers with a Docker Compose template. You control the infrastructure, the network topology, the backup strategy, and the access perimeter.
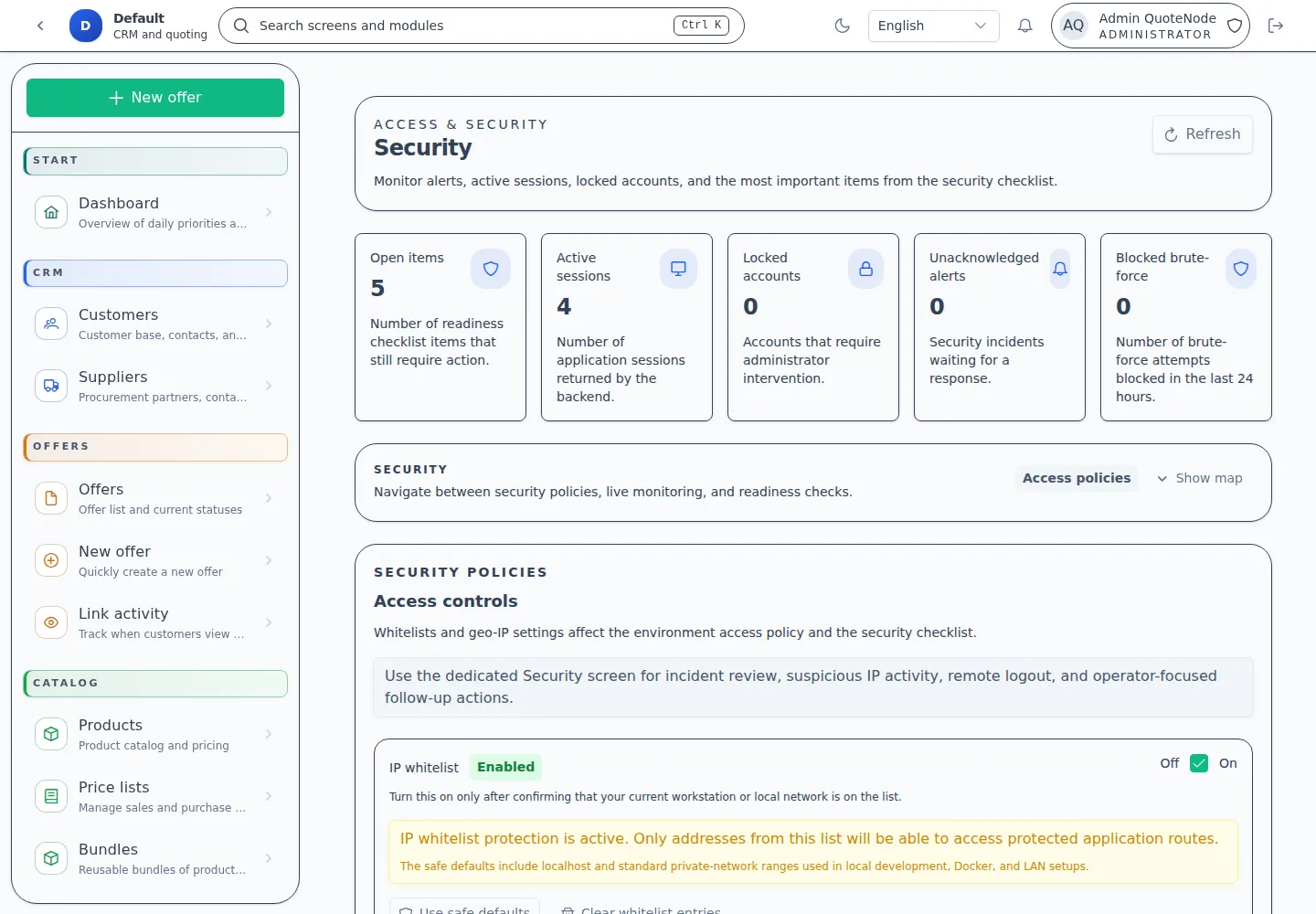
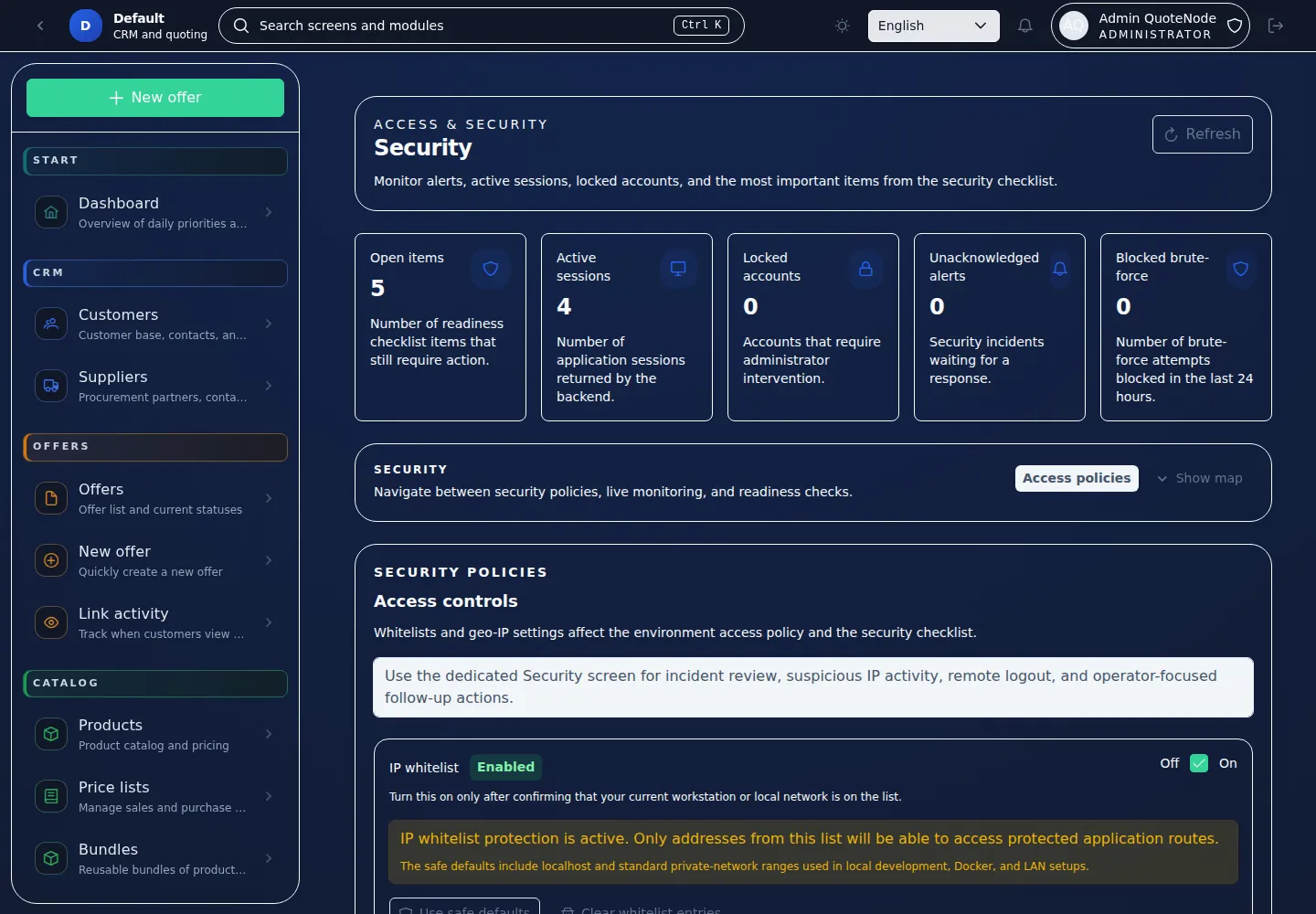
Authentication & Access Control
- Role-based access control (RBAC) with five roles: Admin, Manager, Salesperson, Viewer, and Public (for offer links).
- Per-endpoint permission checks — every API call is authorized against the caller’s role.
- Session-based authentication with encrypted cookies and configurable session lifetime.
- Two-factor authentication (TOTP) — optional for all users, enforceable for administrators.
- Brute-force protection — account lockout after 5 consecutive failed login attempts (30-minute cooldown).
- IP whitelist — optionally restrict application access to specific IP addresses or ranges.
Audit Trail
Every mutation in the system is recorded in an append-only audit log:
- Who performed the action (user ID, role, IP address)
- What changed (entity type, entity ID, before/after state)
- When it happened (server-side timestamp)
The audit log is immutable — entries cannot be edited or deleted, even by administrators. This provides a verifiable chain of custody for every offer, customer record, and configuration change.
Offer Security
Public offer links are protected by multiple layers:
- Cryptographic tokens — 256-bit random tokens, stored only as SHA-256 hashes in the database. The plaintext token is returned once and never stored.
- Optional password protection — offer links can require a bcrypt-hashed PIN.
- Revocable access — any link can be revoked instantly by the salesperson.
- Rate limiting — per-token and per-IP limits prevent abuse (60 opens/hour, 5 actions/hour).
- Bot detection — timing validation and honeypot fields reject automated submissions.
- Interaction tracking — every open, download, reply, and decision is logged with anonymizable IP and GeoIP country code.
Data Protection
- Encryption in transit — TLS for all connections (reverse proxy via Caddy with automatic HTTPS).
- Encryption at rest — delegated to your infrastructure (disk encryption, encrypted volumes).
- Optional PII column-level encryption — when enabled (
ENCRYPT_PII=true), personally identifiable information (customer names, emails, phone numbers, tax IDs) is encrypted with AES-256-GCM at the application layer before being written to the database. Blind indexes (HMAC-SHA256) preserve exact-match query capability without exposing plaintext. A startup validator prevents data corruption from key mismatches or accidental flag changes. - IP anonymization — configurable job to hash IP addresses after N days for GDPR compliance.
- No external dependencies — no third-party analytics, tracking pixels, or CDN dependencies in the default configuration.
- Data retention controls — configurable retention periods for generated documents, audit logs, and tracking data.
Backup & Disaster Recovery
Your data is only as safe as your ability to recover it:
- Automated daily backups — scheduled database dumps and file storage archives run without downtime (configurable via
BACKUP_CRON). - GPG encryption at rest — backups can be encrypted before storage, ensuring that even your storage provider cannot read the data.
- Remote storage — automatic upload to S3, SFTP, Google Cloud Storage, Azure, or any of 70+ providers supported by rclone.
- Integrity verification — every backup includes a SHA-256 checksum manifest for tamper detection.
- One-click download — administrators can download backup archives directly from the admin panel.
- Retention policy — automatic cleanup of old backups keeps disk usage predictable (default: 7 most recent backups).
- Disaster recovery — a dedicated restore script rebuilds a complete instance from a backup file on a fresh server with a single command.
- Monitoring — the admin panel warns if backups are disabled or if no successful backup has been recorded in the last 48 hours.
For the full backup and restore guide, see the Backup & Recovery wiki.
Immutable Offer Snapshots
When an offer is sent, the system captures a complete, immutable snapshot: customer data, all line items, pricing, FX rates, branding, and trading terms. This snapshot is the source of truth for PDF generation and audit purposes.
Snapshots cannot be modified after creation. If an offer is resent, a new snapshot version is created. This provides a verifiable record of exactly what was offered on what date.
Licensing Security
QuoteNode licenses are Ed25519-signed files verified entirely offline. No external server is contacted for license validation. Paid licenses are annual — if a license expires, all features continue to work normally. The only visible change is a “Powered by QuoteNode” badge on client-facing surfaces and a renewal reminder in the UI. No functionality is disabled.